Waterpixel
- approach to simplify (large) images
- is the reduction of the number of pixels (a.k.a image combinatorics) without the alteration of either of
- pixel values (a.k.a spectral information or signature)
- pixel organization (a.k.a pixel topology)
- Practically it is difficult to satisfy the three constraints of
- image size reduction
- information preservation
- structure non-alteration
- Several superpixel paradigms exist:
- waterpixels
- an alternative to superpixel paradigms
- are based on the watershed transformation
- SLIC, Simple Linear Iterative Clustering
- generates superpixels using k-means clustering
- waterpixels
Watervoxel
- Cettour-Janet et al. 2019 (link) outlines their work on Watervoxels,
- is an n-dimensional extension of the waterpixels, as defined in the article
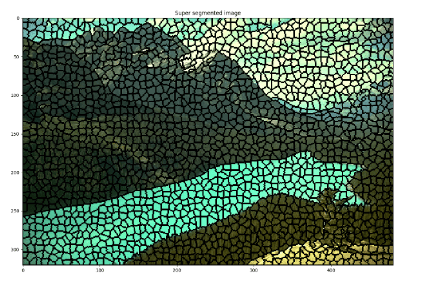
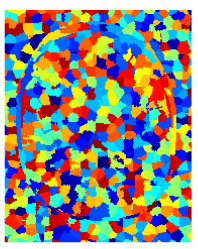
The images below summarize the result of the application of watervoxels to a 2D image and a 3D MRI image.
What are your thoughts on watervoxels? How do you make use of them in your field?
References
Pierre Cettour-Janet, Clément Cazorla, Vaia Machairas, Quentin Delannoy, Nathalie Bednarek, François Rousseau, Etienne Décencière, and Nicolas Passat, Watervoxels, Image Processing On Line, 9 (2019), pp. 317–328. https://doi.org/10.5201/ipol.2019.250
R. Achanta, A. Shaji, K. Smith, A. Lucchi, P. Fua and S. Süsstrunk, “SLIC Superpixels Compared to State-of-the-Art Superpixel Methods,” in IEEE Transactions on Pattern Analysis and Machine Intelligence, vol. 34, no. 11, pp. 2274-2282, Nov. 2012, doi: 10.1109/TPAMI.2012.120.




You must be logged in to post a comment.